These tips can be used for Windows XP and Vista -
Operating systems vary, if in doubt, check with your provider and/or technical support.
Perhaps the term Rogue Security Software is new to you, it is a form of computer malware that deceives or misleads users into paying for the fake or simulated removal of malware. This lucrative and illegal business is rapidly growing.
I have gleaned my information from both the Microsoft and Wikipedia Sites on the Net. There is more detailed information available at both sites.
https://en.wikipedia.org/wiki/Rogue_software
https://www.microsoft.com/security/antivirus/rogue.aspx
Rogue security software mainly relies on social engineering (Social engineering is the act of manipulating people into performing actions or divulging confidential information.) Think of it like a ‘con game' where someone tries to part you and your money. However, it additionally can defeat the security system built into your computer and access a victim's computers.
Many have a Trojan horse to mislead you. Some are disguised as:
- A browser plug-in or extension (typically toolbar)
- An image, screensaver or file attached to an e-mail message
- A Multimedia codec required to play a certain video clip
- A free online malware scanning service
The last one on my list is one that is particularly popular it:
- 1. Tells you that you are ‘infected' with something that sounds or is real.
- 2. Says that they will fix the problem and it is ‘free.'
- 3. You must download their software.
- 4. You must run their software.
- 5. You get back a number that is astronomical - like 863 (or more) errors found. The number may be so high that it, if accurate, would render more computers unusable.
- 6. You must pay for the software (one way to make their money).
- 7. You may even see it run and correct the ‘errors.'
- 8. Your machine may run as before or may even decline.
Once installed, the rogue security software may then attempt to entice the user into purchasing a service or additional software by:
- Alerting the user with the fake or simulated detection of problems
- Displaying an animation simulating a system crash and reboot.
- Selectively disabling parts of the system to prevent the user from uninstalling them.
- Some may prevent anti-malware programs from running.
- Disable automatic system software updates
- And even block access to websites of anti-malware vendors.
- Installing actual malware onto the computer, then alerting the user after "detecting" them. This method is less common as the malware is likely to be detected by legitimate anti-malware programs.
Rogue security software might also appear in the list of search results when you are searching for trustworthy antispyware software.
Rogue security software might also attempt to spoof the Microsoft security update process. Here's an example of rogue security software that's disguised as a Microsoft alert but that doesn't come from Microsoft.
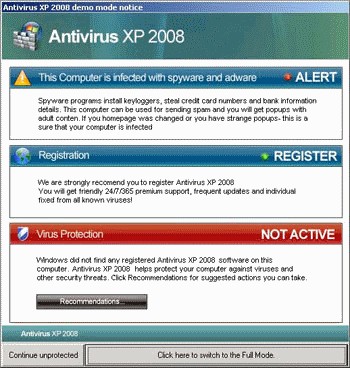
Example of a warning from a rogue security program known as AntivirusXP.
For more information about this threat, including analysis, prevention and recovery, see the Trojan:Win32/Antivirusxp entry in the Microsoft Malware Protection Center encyclopedia.
Another common rogue security program is FakeSecSen:
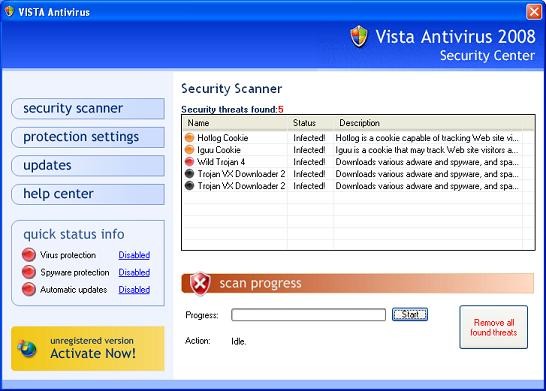
Example of a warning rogue security program known as Fake SecSen.
For more information about this threat, including analysis, prevention and recovery, see the Program:Win32/FakeSecSen entry in the Microsoft Malware Protection Center encyclopedia.
Here is the legitimate Microsoft Windows Security Center:
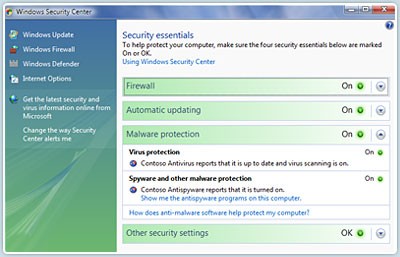
Screenshot of legitimate Microsoft Windows Security Center.
To help protect yourself from rogue security software:
- Install a firewall and keep it turned on.
- Use automatic updating to keep your operating system and software up to date.
- Install antivirus and antispyware software such as Microsoft Security Essentials and keep it updated. For links to other antivirus programs that work with Microsoft, see Microsoft Help and Support List of Antivirus Vendors.
- If your antivirus software does not include antispyware software, you should install a separate antispyware program such as Windows Defender and keep it updated. (Windows Defender is available as a free download for Windows XP and is included in Windows Vista.)
- Use caution when you click links in e-mail or on social networking Web sites.
- Use a standard user account instead of an administrator account.
- Familiarize yourself with common phishing scams.
If you think you might have rogue security software on your computer:
Scan your computer. Use your antivirus software or do a free scan with Windows Live safety scanner. The safety scanner checks for and removes viruses, eliminates junk on your hard drive, and improves your PC's performance.
Check your accounts. If you think you might have entered sensitive information, such as credit card numbers or passwords into a pop-up window or at a rogue security software site, you should monitor your associated accounts. For additional information, see What to do if you're a victim of fraud.
Call PC Safety. Microsoft provides free virus and spyware removal support to Windows customers who think they have an infected computer or have other PC Security questions.
Customers should call 1-866-PC Safety for phone support which is available 24 hours a day 7 days a week.
Customers can also visit https://safety.live.com/ for free online virus and spyware removal.
If you suspect that your computer is infected with rogue security software that is currently not detected with Microsoft security solutions, you can submit samples using the Microsoft Malware Protection Center submission form. For help with isolating undetected samples, call PC Safety.
In 2008, a hacker known as NeoN hacked into a database. Information revealed an affiliate earned $158,000 in a week.
These are a brief listing of the ones that sound so very real that anyone could be a client without knowing it:
- Advanced Cleaner
- Antivirus Pro 2010
- Cleanator
- Doctor Antivirus
- MacSweeper
- MS AntiSpyware 2009
- PC Clean Pro
- Personal Antivirus
- PAL Spyware Remover
- Security Toolbar 7.1 (Clever to say that 7.0 had been improved!!)
- System Antivirus 2008
- UltimateCleaner
- TrustedAntivirus
- TheSpyBot (Spybot - Search & Destroy knockoff)
- WinDefender (not to be confused with the legitimate Windows Defender)
As previously noted, this is just a few of the many malware that is available. I thought these names sounded so realistic. You can see the larger list at the Wikipedia site.
As stated earlier in this blog, much of the information has been directly taken from Microsoft and/or Wikipedia. I felt it was too important than to write my own version. And, may I add, always purchase your software from a reliable source. If in doubt, check your product vendor's site for more information.